SSH Connections in LINUX / UNIX Based Systems
By: Noel D'Souza
INTRODUCTION
SSH connections are used for trusted systems with the help of IP addresses. SSH, or Secure Shell, is a protocol used to securely log onto remote systems. It is the most common way to access remote Linux and Unix-like servers. In this article, we will discuss about access remote systems using SSH connection without asking any password. In SSH communication Public Key & Private Key pairs are used. In this article we are demonstrating how to create Public and Private key pairs and hosting the Public Key on the remote system.
Establish SSH connection using Ubuntu /CentOS based Unix Systems without Password.
Step 1: Check for SSH keys
First, we need to check for existing SSH keys on your Linux based systems.
ex: 192.168.182.128 (System1).
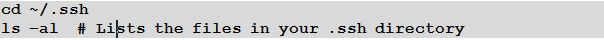
Check the directory listing to see if you have files named either id_rsa.pub or id_dsa.pub. If you don't have either of those files go to step 2.
Step 2: Generate a new SSH key
Type in Linux terminal as:

Screenshot 1:
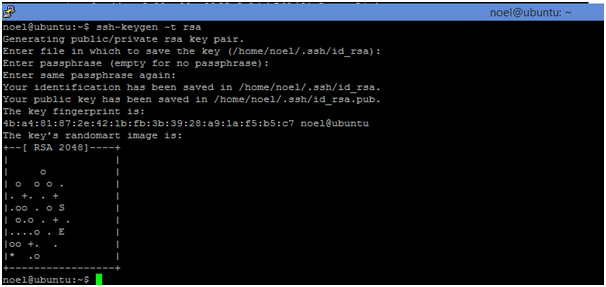
Note: Repeat Step 1 and Step 2 for one more Linux system having IP for example, 192.168.182.141(System2).
Now on both systems System1 and System2 both RSA public and private keys are generated.
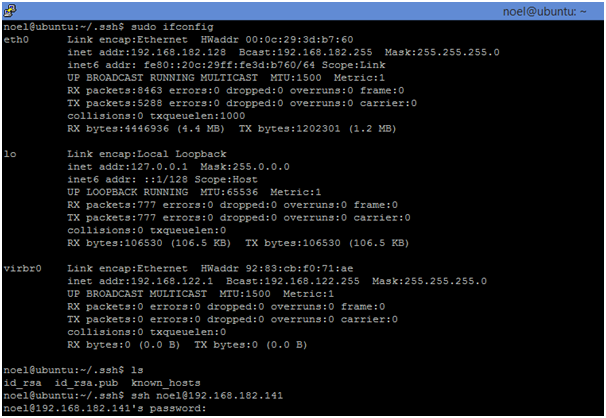
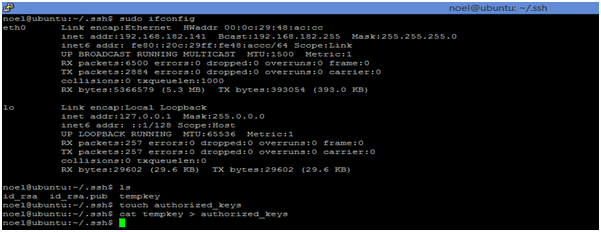
Step 3: Make A SSH Connection from System1 to System2 using the following command and the Screenshot 2 is shown below.
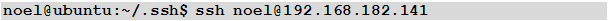
But still it is asking for password while connecting from System1 to System2.
Screenshot 2:
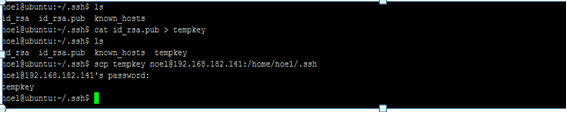
Step 4: Share Your Public id_rsa.pub Key with System2
First you need to copy id_rsa.pub file contents to one more temporary file. Example file name is tempkey and after completion of copy, transfer the tempkey file to System2 by scp Linux command. All these commands are given below and shown in the following Screenshot 3
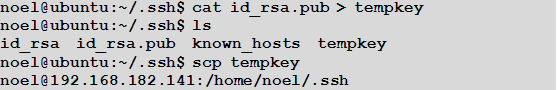
Screenshot 3:
Step5: Establish SSH Connection
Create authorized_keys file in System2 in the path of /home/noel/.ssh/ and append the id_rsa.pub key contents of System1’s tempkey to authorized_keys of System2 (IP: 192.168.182.141). The commands are given below and the Screenshot 4 is follows.
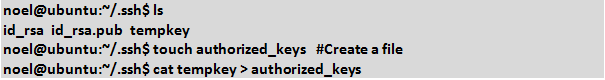
Screenshot 4:
Step 6: Established SSH connection using Ubuntu / CentOS based Unix Systems without Password. The command is given below and the Screenshot 5 follows it.
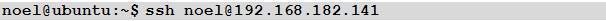
Screenshot 5:
Mr. Noel D'Souza is seasoned programmer in the Linux environment
Linux: split and Paste command << Previous
Our aim is to provide information to the knowledge seekers.





.jpg)